Blockchain security auditors

Security

by

Blockchain

experts

Future-Proof Web3 Audits
Solutions
Smart Contract Audits
Mitigate weak points in your blockchain protocol

DeFi
Borrowing/Lending, Staking, Vesting, Uniswap, AAVE, Compound, Maker, Stargate

L1s and L2s
Interoperability, Gas efficiency, Threat modelling, Dependencies and Bridges

RWA
Valuations, Fractionalization, Ownership, Lock-ups, Insurance and Regulation

DePIN

GameFi
Play-to-earn, Token Utility, Rewards, NFTs, Game Logic and Anti-Cheat systems

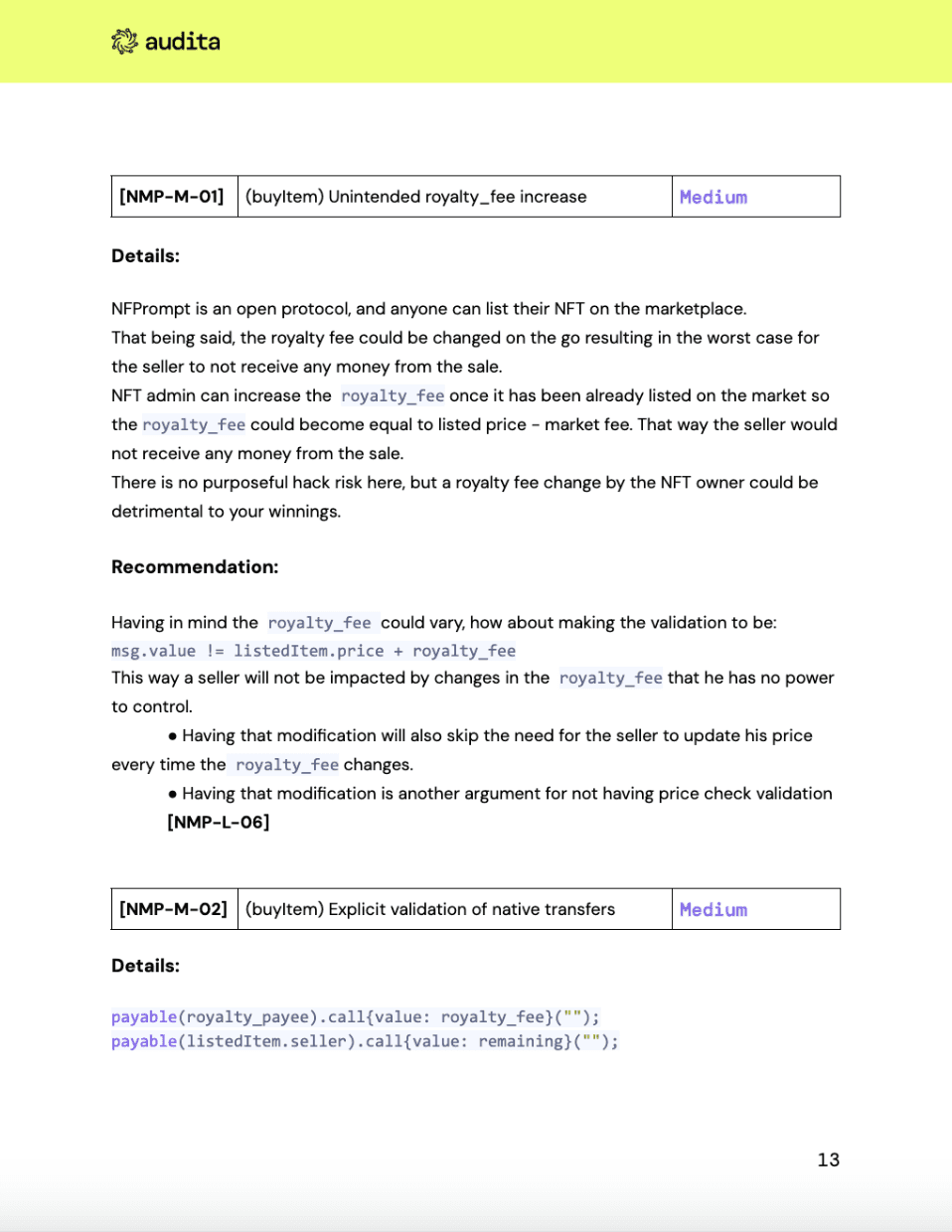
Marketplaces
P2P, Minting, Wallets, Cross-chain, ERC-721/ERC-1155, Interoperability, Oracles
Ecosystem
Partners
Team
The core team behind Audita's smart contracts audits






Pete
Technical Advisor - Rust
With over 7 years of Rust experience, Pete built Matchstick - a Unit Testing Framework for Subgraph devs on The Graph.
notable CLIENTS
Thoughts
Blog
Audita's take on Web3 security